The Tor Project has issued a statement in response to recent claims of a targeted de-anonymization attack on a Tor user. The attack, reportedly a “timing analysis” method, involved the long-retired Ricochet application.
Although the incident raises concerns about the security of Tor’s Onion Services, the project maintains that its network remains healthy and that Tor Browser is still one of the best tools available for anonymous web browsing.
The attack was first brought to public attention through an investigative report by Panorama, which examined how law enforcement agencies, including those in Germany, the U.S., and the U.K., managed to infiltrate the Tor network. The report focused on “timing analysis,” a technique where the size and timing of encrypted data packets are analyzed to trace a user’s activity.
Importantly, this method does not exploit any flaws in Tor’s software but rather leverages surveillance of Tor relays to deanonymize specific targets. The German Federal Criminal Police Office (BKA) is said to have used this method in cases like the takedown of the “Boystown” darknet platform.
The de-anonymization occurred through a sophisticated guard discovery attack, targeting a user of the outdated Ricochet software. Ricochet was discontinued and replaced by a more secure version called Ricochet-Refresh. According to Tor, the old version lacked protections like “Vanguards-lite,” introduced in June 2022 to prevent this specific type of attack. Vanguards-lite was designed to counteract adversary-induced circuit creation that leads to de-anonymization by discovering the user’s Guard relay.
Tor’s statement emphasized that while this attack occurred between 2019 and 2021, the current state of the Tor network is a lot more secure, and updates to the software offer enhanced protections against the described attacks. However, the project called for more transparency and collaboration from those with knowledge of the incident.
Unlike the Chaos Computer Club (CCC), which had access to court documents related to the case, The Tor Project was only given limited information, leading them to request public assistance to fully investigate the details of the attack. The CCC confirmed that law enforcement had used “timing” techniques to deanonymize certain Tor users but raised concerns about the broader implications of such methods being available to authoritarian regimes.
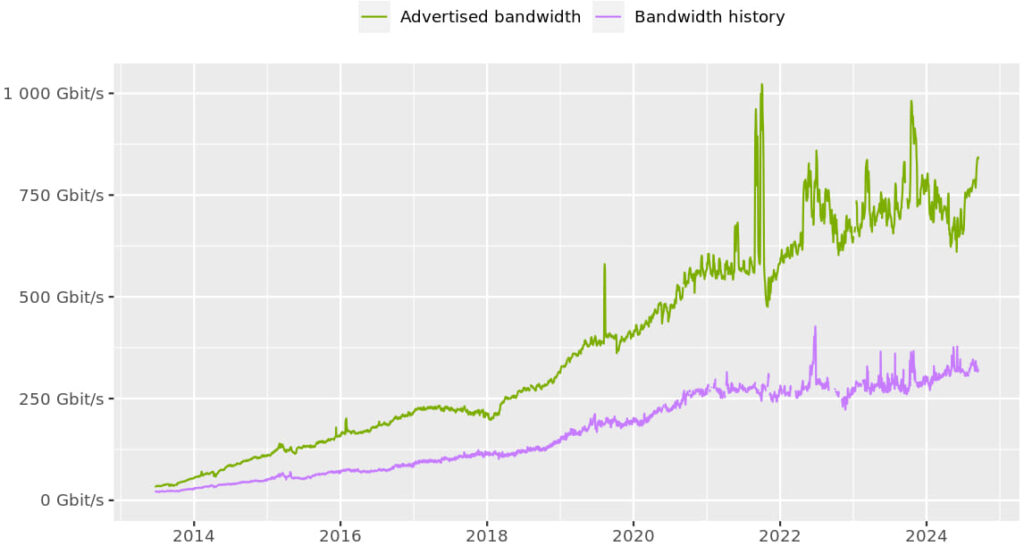
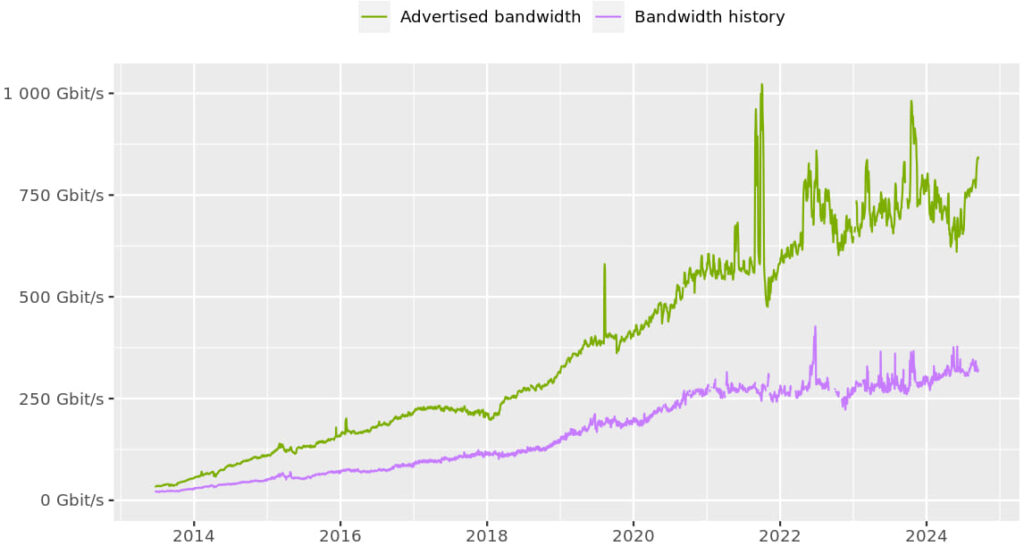
The Tor network, which now boasts over 2,000 exit nodes, remains robust despite the concentration of some nodes in specific countries and hosting centers. Tor’s leadership acknowledged that network diversity—both geographically and operationally—remains a challenge, but ongoing efforts are being made to mitigate risks.
For example, initiatives like the Electronic Frontier Foundation’s (EFF) Tor University Challenge and the introduction of a network health API at DEF CON have been launched recently to bolster the network’s security and performance.
Tor Project
Users concerned about these relevations should ensure they are using the latest versions of Tor Browser and associated tools, which include security features like Vanguards-lite. Also, minimizing connection duration can reduce vulnerability to timing analysis attacks.
Finally, Tor called for volunteers to contribute bandwidth and operate Tor relays to increase geographic and operational diversity, making surveillance harder.